Hackers Getting In
Attackers do not stop looking. The only question is when they find a way in.
Your application is the front door to your private network. Once compromised, attackers can steal files, deploy ransomware, hijack your email, break into your cloud, and more.
Developers lack adequate security training
Apps are built fast to meet business needs – often by developers without training in how hackers actually exploit code.
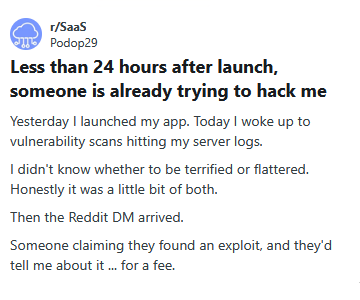
No real-time visibility into security attacks
Most organisations don’t monitor their apps for active threats, meaning breaches can go undetected for years.
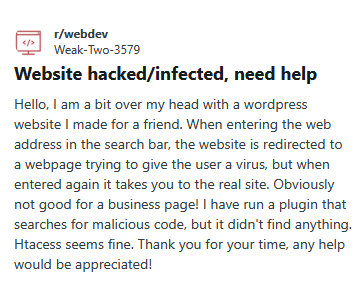
Overreliance on automated security tools
Automated scanners miss logic flaws, complex bugs, and attacks only humans can simulate.
Compliance does not equal real security
Meeting security compliance (like GDPR or PCI-DSS) doesn’t stop hackers – real attacks go far beyond regulatory checklists.
Compliance validates processes and controls at a point in time, but it does not identify exploitable vulnerabilities in your application code or logic.
A firewall limits external traffic, but it cannot stop attacks performed through valid accounts or abused application functionality.
Automated scans detect known patterns, but they cannot identify complex logic errors or authorization weaknesses unique to your system.
Validation in the browser improves usability, but security controls must be enforced on the server side where requests are actually processed.
Hiding features in the interface does not enforce security; proper role and permission checks must be enforced on every backend request.
HTTPS protects data in transit, but it does not prevent broken access control or application logic flaws that expose sensitive information.
Loss of Customer Trust & Data Leakage
A breach can destroy your brand’s reputation, and your data could end up on the dark web.
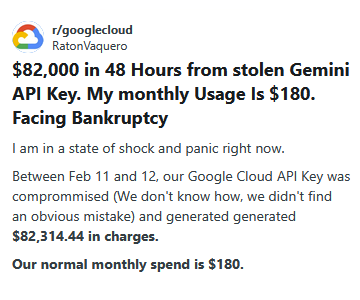
Financial Loss & Fraud
Hackers can steal premium features, bypass payments, and even sell customers’ data, costing businesses millions.

Legal Costs & Regulatory Fines
A data breach exposes you to legal action, regulatory fines, and massive reputational damage.
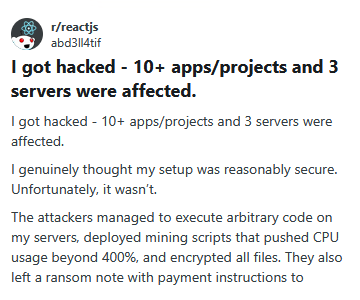
Business Disruption & Downtime
Security incidents can force applications offline, disrupting operations and impacting revenue and productivity.








A breach exposed sensitive user data due to weak security controls, potentially including personal and usage information. This risked complete loss of user trust and opened the door to large-scale account abuse.
One of Australia’s largest breaches exposed highly sensitive medical and personal data of millions of customers. The incident caused severe reputational damage, regulatory scrutiny, and long-term privacy risks for affected individuals.
A breach exposed sensitive student information through compromised systems. This created risks of identity theft and damaged trust in the university’s ability to protect personal data.
Unauthorized access led to potential exposure of user account data and internal systems. This undermined platform integrity and increased the risk of further targeted attacks.
A ransomware attack led to the theft of firmware source code and signing keys. This raised serious supply chain risks, potentially enabling attackers to distribute malicious firmware updates.
Unauthorized access exposed historical personal data of students and staff. The breach posed long-term identity theft risks and highlighted gaps in legacy data protection.
A major breach exposed personal details, including IDs, of millions of customers. This led to widespread fraud risks, regulatory fallout, and severe reputational damage.
A cyberattack compromised millions of user records, including emails and hashed passwords. The breach increased the risk of credential stuffing attacks and weakened user trust globally.
Attackers gained deep access to internal systems through social engineering. This exposed sensitive data and demonstrated critical weaknesses in internal security controls.
CWE – Most Dangerous Software Weakness by Vulncheck
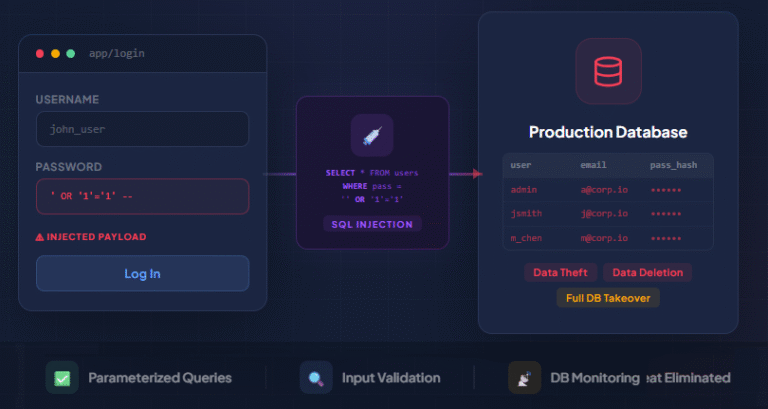
Injection attacks are security vulnerabilities in which attackers inject malicious code into an application (such as SQL, command, or script injection) to manipulate databases and execute unauthorized commands.
Broken authentication is a security vulnerability in which flaws in login systems (such as weak passwords, session mismanagement, or credential leaks) allow attackers to gain unauthorized access.
Sensitive Data Exposure is a security vulnerability in which improperly protected sensitive information (such as passwords, credit card details, or personal data) is accidentally leaked or made accessible.
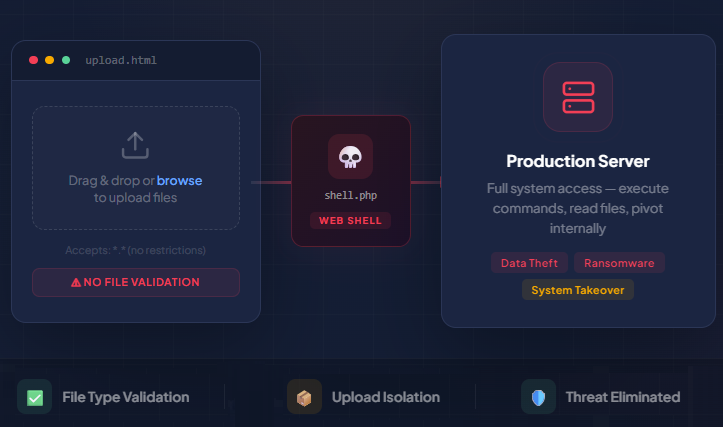
Insecure file upload is a vulnerability where a system improperly handles uploaded files, allowing attackers to upload malicious files (like scripts or executables) that can lead to data breaches and server compromise.
XSS (Cross-Site Scripting) is a security vulnerability where attackers inject malicious scripts into web pages viewed by users, allowing them to steal data, hijack sessions, or manipulate the website's content.
Security misconfiguration is a vulnerability that occurs when an application, server, or database is improperly configured, leaving it exposed to attacks due to default settings or incomplete configurations.
Broken access control is a security flaw where users are able to access resources or perform actions that they are not authorized for, often due to inadequate restrictions.
Using known vulnerable components refers to the practice of incorporating outdated or insecure software libraries, frameworks, or plugins into an application, which can expose the system to known attacks.
Insecure data storage is a vulnerability where an application stores sensitive information (such as credentials or tokens) without adequate protection, making it accessible to unauthorized users.
Find Hidden Weaknesses Before Hackers Do
Penetration testing uncovers hidden weaknesses in your system before real attackers can exploit them, allowing you to address issues promptly.
Avoid Costly Data Breaches
A single cyberattack can lead to stolen customer info, lawsuits, or fines. Penetration testing helps prevent this.
Meet Legal Requirements & Compliance in Australia
Industry standards (such as ISO 27001) and Australian regulations, including the ACSC Essential Eight and the Privacy Act 1988, mandate regular security checks. Penetration testing ensures compliance and helps avoid fines and data breaches.
Build Customer Trust
Customers feel safer knowing you care about their data, and It boosts your reputation as a secure and reliable business.

Penetration
testing
Performing at least an annual penetration test to uncover critical security flaws in your application before attackers do.
- Offered By Penva Security
Penetration Testing
as a Service (PTAAS)
Using a PTaaS approach to ensure every update and new release is tested for vulnerabilities before it reaches production.
- Offered By Penva Security
Hire dedicated
pentesters
Hiring dedicated penetration testers to manage the ongoing security of your application and Infrastructure.
- Offered By Penva Security
Bug bounty
programs
Launching a bug bounty program, incentivising security researchers to find and report vulnerabilities.
A professionally signed and certified report that proves your system was independently tested
Satisfy government, industry, and insurance requirements with a report that proves your due diligence.
Close enterprise deals faster with proof of security, while giving your developers real examples from your own product to learn and improve from.
Vulnerabilities, ranked by severity, with plain-language descriptions and exactly what needs to be fixed first.
Show your board, investors, and enterprise clients a concrete document proving your platform is actively secured.
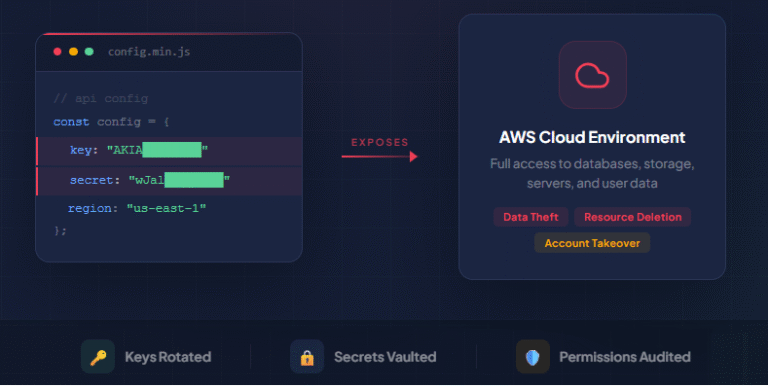
The exposure was critical; anyone on the internet could silently access sensitive systems. We immediately advised rotating the keys, moving all secrets to secure vaults, and auditing cloud permissions.
We immediately recommended strict file type validation, scanning uploads for malware, and isolating uploads from critical systems.
We recommended parameterized queries and input validation on the backend. After remediation, the application was secured against data breaches.
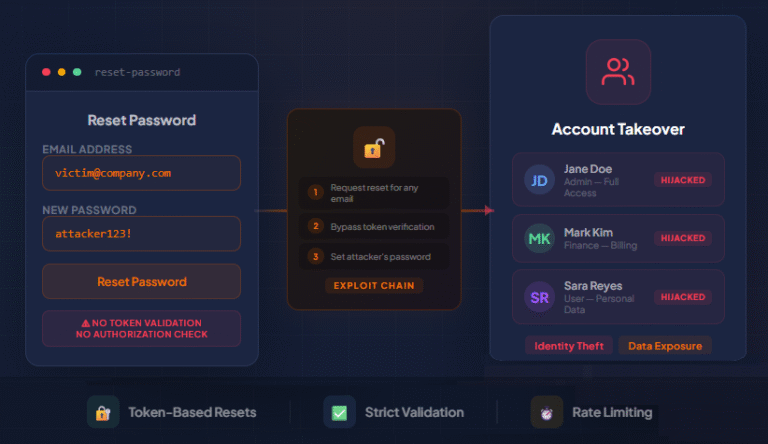
This risked exposure of sensitive personal data, financial information, or administrative controls. We recommended implementing token-based resets, strict validation, and rate limiting.
We have partnered with organizations across critical sectors, including finance, education, e-commerce, and healthcare, to enhance their security posture, meet compliance requirements, and confidently pass audits.
We’ve identified critical vulnerabilities in 70% of tested applications, including server compromises and leaked credentials, and helped secure their applications and infrastructure.
Accreditations & Certifications

Michael Wendland
Partner at Bonsai
Reliable and professional penetration testing partner
Penva Security provided a quick and efferent pentest report that satisfied our needs and certification criteria. I would highly recommend them for penetration testing, and will be using his services again in the future.
Stuart Cox
Creative Director at NorthBase
Professional, communicative, and highly reliable testers
Penva Security conducted a penetration test of our webapp and produced a report of security issues. The team was professional and communicated well throughout, including giving us the expected timeline for the work and keeping us up-to-date as we progressed. The report was well written and I can recommend them to anyone looking for penetration testing.
Daniel Scocco
Founder at InstaDelivery
Working with third or forth time with Penva Security
This is the third or fourth time we work with Penva Security. They always delivers timely and great work. One of the best security experts I know.
Brand Name
Certification
Certification Worth
OSCP by Offensive Security
OSCP+ by Offensive Security
The OSCP (Offensive Security Certified Professional) is a highly regarded certification that validates practical penetration testing skills and is globally recognized by employers and regulators.
CREST Practitioner Security Analyst (CPSA)
CREST Registered Penetration Tester (CRT)
CREST partners with national bodies in the UK, US, Australia, and Singapore, ensuring global recognition and compliance with the highest cybersecurity standards.

CRTO by Zero-Point Security
This certification demonstrates the ability to think and act like a real attacker, simulating advanced cyberattacks to help organizations identify and remediate hidden weaknesses before they can be exploited.
Penva Security holds globally recognised, specialized penetration testing certifications that take years to earn.